Computer worms can wreak havoc on your system if you don’t protect it adequately. Worms spread by exploiting vulnerabilities in programs or the device’s operating system. While different worms work differently, the effects can be disastrous, ranging from slowing down and crashing systems to the theft of your confidential data or more malware installation.
Installing malware protection that regularly scans and updates your system may help you quickly identify security flaws and potential threats. It can help you rest easy knowing that you’re taking proactive measures to stop any malicious activity before it happens.
Keep reading to learn more about the dangers of worms and how you might better protect yourself.
Table of contents
How Does A Computer Worm Work?
The term “computer worm” refers to a self-replicating malicious software program that spreads across networks by exploiting security vulnerabilities in software and computers.
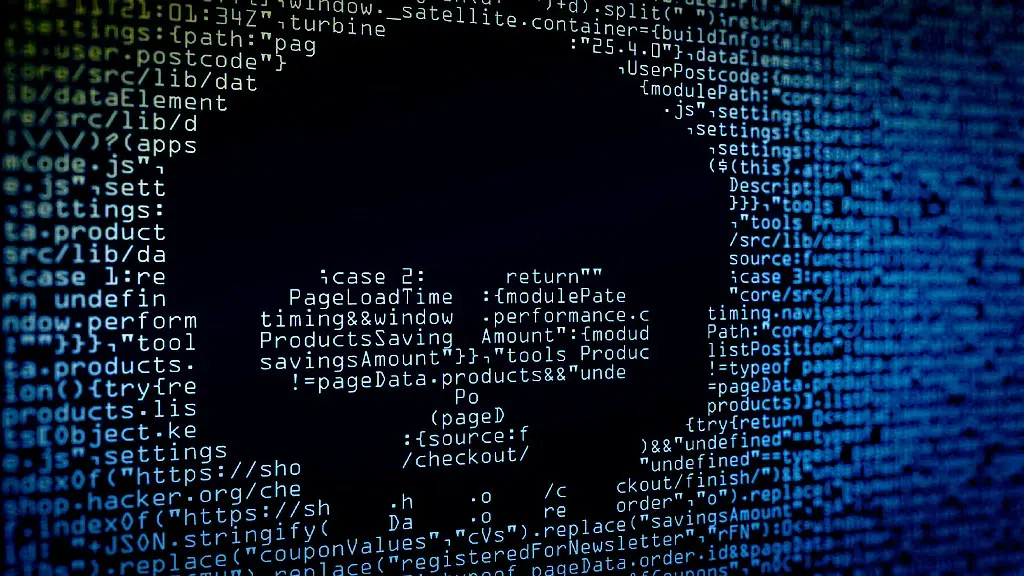
The worm scans for vulnerabilities in systems on the internet and takes control of them.
Once it takes control, it begins duplicating itself, creating multiple copies that spread further across the internet. It repeats until it spreads across all computers.
The Difference Between A Worm And A Virus
Computer worms are often confused with viruses because they both spread across networks and can cause damage to computers. However, there are some key differences between them.
Unlike viruses, worms don’t need an existing application to attach themselves to. Instead, they create their programs to replicate.
A virus also requires user action, like clicking on an email attachment or downloading files, to spread. On the other hand, a worm can spread without user intervention.
Types Of Computer Worms
There are several different types of worms out there. Here are a few common examples.

Network Worms
Network worms are designed to spread themselves by exploiting vulnerabilities in PC networks. Once a network worm gains access to a PC, it will scan the network for other computers vulnerable to the same exploitation.
Then, it attempts to infect those computers too. Worms spread using various methods, including malicious emails, exploiting operating system vulnerabilities, and using weak passwords.
Furthermore, they can spread via USB drives and shared drives. As an example, WannaCry ransomware exploited a Microsoft Windows vulnerability to spread rapidly across a network, encrypting data on infected computers and gaining access to computers through weak passwords.
Email Worms
Email worms are designed to spread through emails containing infected attachments or links to infected websites. When a user opens the email attachment or clicks the link in their computer, the worm spreads to other contacts in the user’s address book.
The email’s subject line usually entices the user to open the email and the attachment. It may be like “You’ve got a postcard” or “Re: Approved.” Your email may contain a message like “Thank you for your order” or “Congratulations, you’ve won.”
Internet Worms
Internet worms are designed to spread by exploiting vulnerabilities in web servers. Once an Internet worm gains access to a web server, it replicates itself on the server and attempts to infect more visitors with the worm. In most cases, internet worms spread through security holes in web browsers.
Often, they carry malicious code that allows them to propagate from one system to another. Internet worms use vulnerabilities in web browsers like Internet Explorer, Chrome, and Firefox to download and install malicious programs.
File-Sharing Worms
File-sharing worms spread through file-sharing networks. When a user downloads and opens a file that contains a file-sharing worm, the worm will begin spreading itself to other users on the network.
The worm copies itself to the computer and searches for other computers. After finding them, it sends a copy of itself. The file-sharing worm can then spread to other users on connected networks.
Preventing A Worm Attack
Keeping your PC safe from a worm attack requires more than just staying vigilant online. Making sure you have malware protection may be just as important. Antivirus software and comprehensive malware protection software can provide an extra layer of security against threats like worms, ransomware, and phishing.
Keep your software up-to-date and use strong passwords to protect your accounts. You should also avoid clicking on suspicious links or emails. Consider programs that include firewalls, web shields, ransomware protection, and other advanced security features.
These additional layers of defense may help keep your system secure from malicious attacks, allowing you to continue surfing the web with peace of mind.
Final Thoughts
Computer worms can devastate your digital life, from stealing your personal information to corrupting or deleting stored files.
Regularly downloading security updates, backing up your files on external hard drives, and scanning for malware at least once a week may help ensure your computer remains secure.
Everyone deserves to have a secure home network, and with the proper steps, you may be able to limit the dangers of the web.
Also Read: